Adopt ZTNA now and we’ll buy out your VPN support contract*
You’ve been trying to make your legacy VPN meet today’s network security needs, but it’s becoming clear that security vulnerabilities, and the new cyberattacks exploiting them, are a network security risk. To make matters worse, you are stuck in a contract.
We’re offering you a way out, and a way to start your Zero Trust journey without delay. If you license with us by the end of June 2022, we’ll buy out your VPN contract so you can implement Zero Trust Network Access – you can verify users, validate devices, and provide 1:1 application access.

Your Challenge:
Using VPNs to keep your distributed workplace connected is complicated and insecure
Complex Configuration
Ransomware Spread
Lateral Movement
VPN Infiltration
Remote access got more complicated – and expensive – with the accelerated shift to remote work. Add the movement of applications to the cloud to the mix, and IT teams have a real, ongoing challenge on their hands.
VPN-based approaches don’t scale, are complex to set-up and manage, frustrate users, grant excessive access, and expose your network to attacks.

Our Solution:
Easily connect users to apps using a secure ZTNA approach
Zero Trust Network Access
Automatic Policy Builder
Continuous Visibility
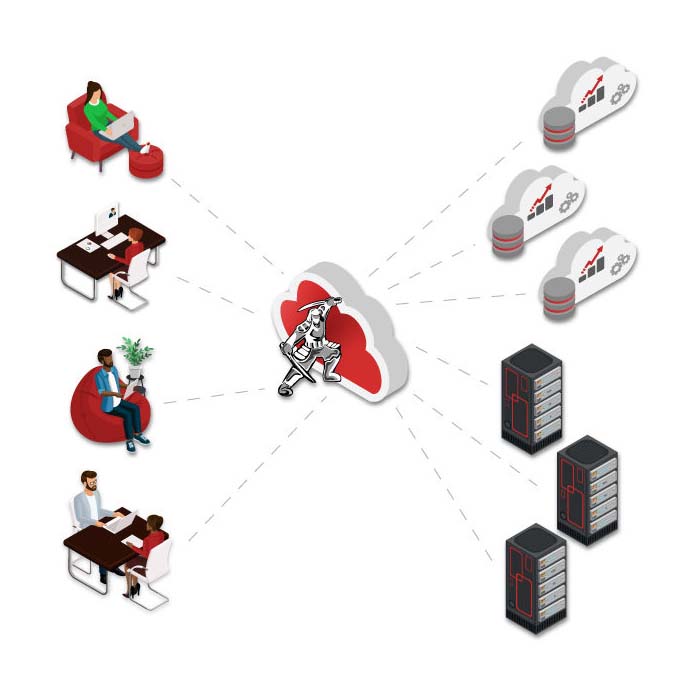
ZTEdge Zero Trust Network Access (ZTNA) capabilities make it easy to connect users, even 3rd parties, to any app or resource, regardless of location (cloud or on-prem). No network reconfiguration is required, and you can integrate with the identity solution you already use or utilize ZTEdge’s built-in identity capabilities.
With our patent-pending Automatic Policy Builder, you can easily set granular access policies, and let the software analyze network traffic to create recommended configurations.
Dashboards provide continuous fine-grain visibility on user behavior and network traffic:
- Easily connect users to apps, boosting productivity and accelerating digital transformation initiatives
- Save time on manual configuration and administration, freeing up IT resources
- 1:1 microsegmented access secures your apps and reduces lateral movement and ransomware risks
Jumpstart Your Move to Zero Trust by Implementing ZTNA Now
Ditching your VPN for Zero Trust Network Access (ZTNA) just became a no-brainer.
- ZTNA is far more secure than VPNs, whose vulnerabilities are making ransomware headlines weekly, resulting in millions of dollars in losses for organizations.
- Implementation of ZTEdge ZTNA is quick and simple.
- We’ve architected ZTEdge to be cost effective – approximately half of competitive alternatives – and we’re passing the savings on to you.
- To sweeten the deal, this program covers the cost of your existing VPN contract.*
How can you qualify?
- Minimum 100 ZTEdge ZTNA new licenses required to qualify
- Contract for ZTEdge solution must be for a 36-month commitment
- Signed contract must be received by Ericom no later than 6.30.2022
*Businesses get up to 100% user subscription discount to cover the remaining term of their VPN support contract for up to 12 months with a 36-month term commitment. Discount is applied against the newly licensed number of ZTEdge ZTNA licenses, up to the number of replaced VPN licenses Other restrictions may apply. Contact us for full details by completing the form below.
Learn More About the ZTEdge Buy-out Program
Why ZTEdge?
Simple, affordable Zero Trust capabilities in a single integrated cloud platform
Simple
Comprehensive
Afforable
ZTEdge, designed to meet the unique security requirements of small businesses and medium size enterprises, delivers a comprehensive set of Zero Trust security capabilities via a high-performance, resilient cloud platform. A cloud-native architecture and flexible global PoP infrastructure make ZTEdge highly efficient, allowing us to pass significant cost savings along to our customers.
Let us accelerate your move to Zero Trust.