Zero Trust Remote Application Access
Zero Trust Network Access (ZTNA) is flexible, scalable and manageable remote access. With ZTNA, you can verify users, validate devices and provide 1:1 access to private applications.
Complex Configuration
Ransomware Spread
Lateral Movement
VPN Infiltration
Keeping your distributed workplace connected is complicated and insecure
Remote access got more complicated – and expensive – with the accelerated shift to remote work. Add the movement of applications to the cloud to the mix, and IT teams have a real, ongoing challenge on their hands.
Zero Trust Network Access
Automatic Policy Builder
Continuous Visibility
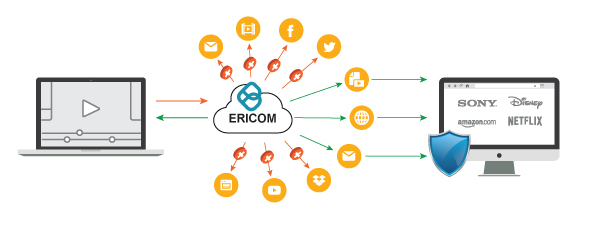
Easily connect users to apps using a secure ZTNA approach
Ericom Zero Trust Network Access (ZTNA) capabilities make it easy to connect users, even 3rd parties, to any app or resource, regardless of location (cloud or on-prem). No network reconfiguration is required, and you can integrate with the identity solution you already use or utilize Ericom’s built-in identity capabilities.
With our patent-pending Automatic Policy Builder, you can easily set granular access policies, and let the software analyze network traffic to create recommended configurations.
Dashboards provide continuous fine-grain visibility on user behavior and network traffic:
- Easily connect users to apps, boosting productivity and accelerating digital transformation initiatives
- Save time on manual configuration and administration, freeing up IT resources
- 1:1 microsegmented access secures your apps and reduces lateral movement and ransomware risks
Clientless ZTNA Security for Unmanaged Devices and BYODs
Secure access to enterprise web and cloud applications by 3rd party contractors and remote staff using unmanaged devices and BYODs
Unmanaged devices used by contractors and 3rd parties are a significant challenge for IT and Security teams. These groups need access to corporate apps, and the data inside them, to do their jobs. But because they are unmanaged, they represent a unique risk. If one of these devices is compromised, it can deliver malware to apps, leading to lost data, downtime, or worse. Unfortunately, the unmanaged nature of the devices also leaves the organization exposed to any of the 3rd party users who represent an insider threat.
Ericom Web Application Isolation allows you to enforce important data sharing controls on unmanaged devices that access your applications. You can limit data sharing (upload/download, screen printing, clip-boarding, etc.) within your apps by users, groups, device types, locations, and more. Data loss prevention built into the solution protects enterprise assets from leaking to untrusted devices. These controls can be enforced on private corporate web apps, or on access to public SaaS applications like Salesforce, ServiceNow, Box, or Office 365.
Additionally, Ericom Web Application Isolation can be used to secure exposed surfaces of web apps, protecting them from compromised devices and bad actors, while ensuring your legitimate users have full access. Hackers or infected machines that attempt to probe web apps, seeking vulnerabilities to exploit, have no visibility to page source code, developer tools or APIs. Instead, they will only see a few lines of Ericom Remote Browser Isolation HTML.
Resources View All
Ericom Security Solutions Summary
Download PDFWeb Application Isolation Case Study - Multinational IT Consultancy
Download PDFSecuring Instant Messenger Solution Sheet
Download PDF